- The Wasabi protocol was exploited for over $5 million in exploits throughout Ethereum, Base, Verachain, and Blast.
- Compromised administrative keys from Wasabi deployer wallets had been used to improve contracts and exfiltrate funds.
- This exploit represents a big ongoing threat for directors and will elevate new issues after greater than $600 million in losses in April 2026.
On April 30, 2026, the Wasabi protocol suffered an enormous exploit that resulted in over $5 million being leaked throughout Ethereum (ETH), Base, Berachain, and Blast. Safety corporations Blockaid, CertiK, and PeckShield confirmed that attackers used compromised administrative keys from deployer wallets to improve contracts and steal funds from liquidity swimming pools and vaults. The group warned customers to cease interacting with all contracts.
Wasabi Protocol Victims of Multi-Chain Exploit Costing Over $5 Million
In line with sources, PeckShield, Blockaid, and CertiK have reported that attackers exploited Wasabi Protocol, a DeFi derivatives platform, exfiltrating greater than $5 million throughout ETH, Base, Berachain, and Blast. This assault focused liquidity swimming pools and vaults throughout these networks. Key on-chain particulars embody:
- Attacker tackle: 0x02228b0afcdbEdf8180D96Fc181Da3AF5DD1d1ab
- Privileged Entry/Contract Improve Transaction: 0x985b4cde1075c67841d0f9fd897da34c9da53d77f6e23b5a19653ebff4a6fac1
Particularly, the attackers leaked a number of property together with WETH, PEPE, MOG, USDC, ZYN, REKT, cbBTC, AERO, and VIRTUAL. They consolidated the stolen funds into ETH, bridged them to the Ethereum community, and distributed them throughout a number of addresses.
How a compromised administrative key enabled the exploit
The basis trigger was that the executive keys related to the Wasabi deployer pockets (an externally owned account (EOA) often called wasabideployer.eth) had been compromised and exploited by the attackers. This EOA owned the one ADMIN_ROLE within the protocol’s entry management framework.
The attacker used the leaked key to grant ADMIN_ROLE to an attacker-controlled helper contract. Blockaid and CertiK stated that “the compromised administrative keys allowed attackers to realize privileged entry by Wasabi deployer wallets, improve core techniques, and exfiltrate funds.”
The attackers carried out a UUPS improve to the Wasabi protocol’s core contracts, together with the LongPool, ShortPool, perp vault, and Vault contracts, gaining elevated privileges that allowed them to empty liquidity and underlying property throughout a number of chains. In line with a BlockSec report, wallets funded with Twister Money acquired administrator-level roles and actively participated in transactions throughout the protocol’s key swimming pools and vault techniques.
What are the broader implications for DeFi safety and what’s subsequent?
The incident ended one of many worst months on document for DeFi exploits. In April 2026, greater than 25 incidents resulted in losses of greater than $600 million. Wasabi protocol assaults may additional erode belief and lift new issues concerning the safety of administrative keys throughout the ecosystem.
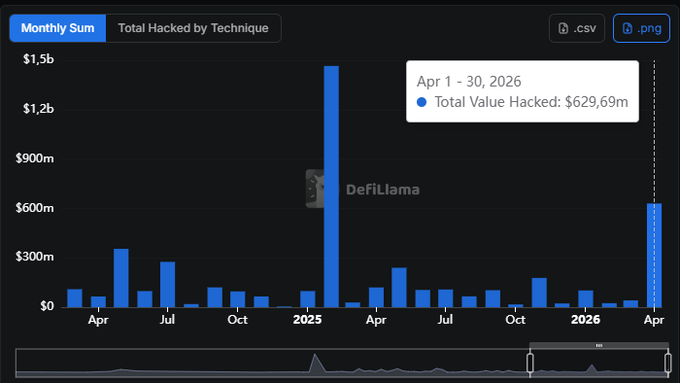
sauce: Defilama
This exploit follows large-scale breaches like Kelp DAO ($293 million) and Drift Protocol ($285 million). These repeated assaults spotlight ongoing dangers round administrative key safety, privileged entry, and cross-chain infrastructure.
In the meantime, Wasabi Protocol continues to analyze the incident and urges customers to keep away from all contracts till additional discover. Virtuals Protocol has frozen associated margin deposits as a precautionary measure. Trade consultants are actually calling for stronger multisig wallets, timelock mechanisms, and improved operational safety to stop future single factors of failure.
Associated: Rhea Finance loses $7.6 million in pretend token pool assault
Disclaimer: The data contained on this article is for informational and academic functions solely. This text doesn’t represent monetary recommendation or recommendation of any form. Coin Version is just not liable for any losses incurred on account of the usage of the content material, merchandise, or companies talked about. We encourage our readers to carry out due diligence earlier than taking any motion associated to our firm.













Leave a Reply